
In 2026, paying with a tap feels effortless. You unlock your phone, confirm with your fingerprint or face, and the transaction is done. No physical card. No typing long numbers. Just speed and convenience.
But behind that simplicity lies a growing cybersecurity concern: Digital Wallet Attacks.
As more people store debit cards, credit cards, and payment tokens inside mobile wallets, cybercriminals are shifting their focus. Instead of stealing physical cards, they now target the digital versions stored on our phones, smartwatches, browsers, and apps.
And unlike traditional fraud, these attacks often happen silently.
What Are Digital Wallet Attacks?
Digital Wallet Attacks refer to cybercrimes where hackers compromise stored payment cards, authentication tokens, or wallet credentials to make unauthorized transactions.
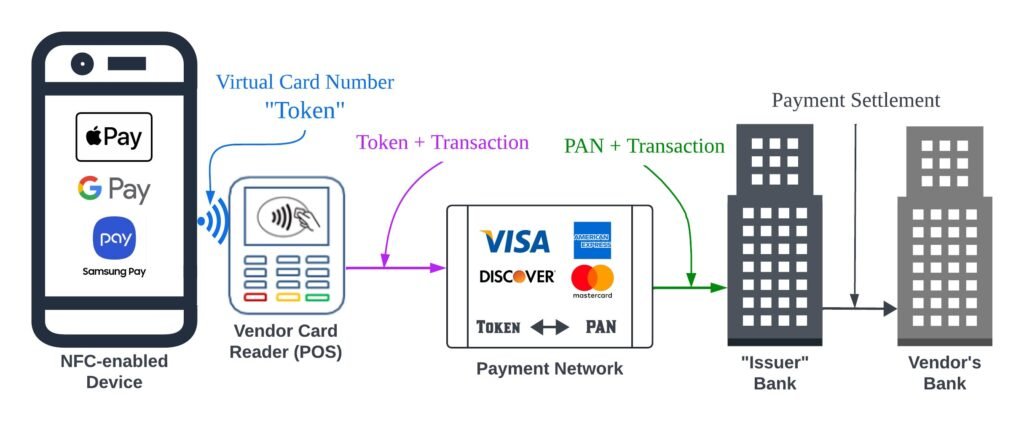
Digital wallets such as Apple Pay, Google Wallet, Samsung Wallet, and PayPal store encrypted versions of your payment cards. These platforms use tokenization, meaning your actual card number isn’t directly shared during transactions.
However, while tokenization increases security, it doesn’t make wallets invincible.
Instead of attacking the bank, criminals attack the user.
That shift is what makes Mobile Wallet Attacks so dangerous in 2026.
Why Digital Wallets Have Become Prime Targets
Digital wallets now store more than just payment cards. Many users keep:
- Multiple credit and debit cards
- Boarding passes
- Loyalty cards
- Identity documents
- Buy-now-pay-later accounts
- Cryptocurrency access
This concentration of financial data creates a high-value target.
Cybercriminals understand that compromising one wallet can unlock access to multiple accounts. That’s why Digital Wallet Attacks are increasing globally.
Unlike old school card skimming, today’s fraud happens through:
- Phishing pages
- Malware
- SIM swapping
- Account takeover attempts
- Social engineering
The technology is secure. The human layer is not.
How Digital Wallet Attacks Actually Happen
Most people imagine hackers breaking encryption. In reality, Digital Wallet Attacks rarely involve cracking security systems directly.
Instead, attackers use indirect methods.
1. Account Takeover
If criminals gain access to your email or cloud account, they may reset wallet credentials.
For example:
- They trigger a password reset.
- Intercept verification codes.
- Log into your wallet account.
- Add a new device.
- Approve transactions.
Because the login appears legitimate, fraud detection systems may not immediately block it.
This is one of the fastest growing forms of Digital Wallet Attacks.
2. SIM Swapping
In a SIM swap attack, criminals convince a mobile carrier to transfer your phone number to their SIM card.
Once they control your number, they can:
- Receive OTP verification codes
- Reset wallet passwords
- Approve new device registrations
Since many wallets rely on SMS-based authentication, SIM swapping fuels Digital Wallet Attacks worldwide.
3. Phishing for Wallet Credentials
Phishing has evolved dramatically.
You might receive:
- A fake wallet suspension alert
- A “security verification” email
- A payment failure notice
The message directs you to a cloned login page.
You enter your credentials.
Attackers capture them instantly.
Modern phishing sites are polished, mobile-optimized, and convincing. This method remains a major driver of Mobile Wallet Attacks
4. Malware on Mobile Devices
Malicious apps disguised as:
- Flashlight tools
- Battery optimizers
- Fake banking apps
- QR code scanners
can secretly monitor screen activity, capture keystrokes, or overlay fake login pages.
If a compromised device stores a wallet, attackers can intercept authentication tokens.
These malware-driven Digital Wallet Attacks are especially dangerous because users may not notice unusual behavior.
The Hidden Weak Point Token Provisioning
Digital wallets use tokenization, replacing your real card number with a secure token. That sounds safe and it usually is.
But attackers don’t need your original card number if they can:
- Trick banks into approving a new token
- Add your card to their own device
- Pass identity verification checks
Some Mobile Wallet Attacks focus on social engineering banks during the token approval process.
Criminals may:
- Call customer service pretending to be you
- Provide leaked personal information
- Bypass verification questions
Once a token is issued to the attacker’s device, they can make contactless payments freely.
Why Digital Wallet Attacks Are So Effective
Technology plays a role. Psychology plays a bigger one.
Digital Wallet Attacks succeed because they exploit:
Trust – People trust well-known wallet brands.
Speed – Transactions happen instantly.
Convenience – Fewer security checks mean less friction.
Overconfidence – Users assume tokenization makes them untouchable.
The more seamless the experience, the easier it is to overlook warning signs.
And once a digital wallet is compromised, losses can escalate quickly.
Warning Signs of Digital Wallet Attacks
Many victims miss early indicators.
Watch for:
- Login alerts from unknown devices
- OTP codes you didn’t request
- Notifications about new cards being added
- Small “test” transactions
- Sudden SIM deactivation
These are often the first stages of Mobile Wallet Attacks.
Ignoring them can lead to larger financial damage.
How to Protect Yourself
Security does not require technical expertise. It requires habits.
Here’s how to reduce the risk of Mobile Wallet Attacks
1. Use App-Based Authentication
Avoid SMS-only verification. Use authenticator apps whenever possible.
2. Lock Your SIM
Ask your mobile carrier to enable SIM lock or port-out protection.
3. Avoid Public Wi-Fi for Payments
Unsecured networks increase interception risks.
4. Monitor Wallet Activity Regularly
Check transaction history frequently, even for small amounts.
5. Install Apps Only from Official Stores
And review permissions carefully.
6. Enable Device-Level Security
Use strong passcodes, biometrics, and automatic screen locking.
7. Never Share Verification Codes
No legitimate company will ask for them.
Simple steps dramatically reduce vulnerability to Digital Wallet Attacks.
The Role of Artificial Intelligence in Wallet Fraud

Artificial intelligence has amplified fraud sophistication.
Criminals now use AI to:
- Generate convincing phishing emails
- Clone customer service voices
- Automate credential stuffing attacks
- Analyze leaked databases
Some advanced Mobile Wallet Attacks even use AI chatbots to impersonate support agents in real time.
Fraud is no longer random.
It is strategic, data-driven, and automated.
The Future of Wallet Security
Security providers are responding with:
- Behavioral biometrics
- Device fingerprinting
- Real-time fraud detection
- Transaction risk scoring
- Token lifecycle monitoring
Still, no system is flawless.
As defenses improve, attackers adapt.
Digital Wallet Attacks will continue evolving just like every other form of cybercrime.
Conclusion
Digital wallets may define the future of payments, but their biggest weakness isn’t technology it’s trust. In 2026, attacks focus on human behavior, not broken encryption. A single careless click, shared code, or ignored alert can open the door to fraud. Stay aware, question unexpected requests, and protect your digital wallet the way you protect your physical one if not more.
