Why Cybersecurity Testing Matters in 2026
As businesses increasingly rely on digital infrastructure, protecting systems from cyber threats has become more important than ever. Organizations store sensitive information such as financial data, customer records, and internal communications online, making them attractive targets for cybercriminals.
To protect these systems, companies regularly conduct security testing to identify vulnerabilities before attackers can exploit them. Two commonly used cybersecurity testing methods are Vulnerability Assessment and Penetration Testing (VAPT). While these terms are often used together, they are not the same.
Understanding the difference between vulnerability assessment and penetration testing is essential for cybersecurity professionals, IT teams, and organizations aiming to strengthen their security posture. Both methods help detect weaknesses, but they serve different purposes and involve different approaches.
This article explains what each method involves, their key differences, and why organizations should use both as part of a comprehensive cybersecurity strategy.
What Is Vulnerability Assessment in Cybersecurity?
A Vulnerability Assessment is a systematic process used to identify, analyze, and prioritize security vulnerabilities in computer systems, networks, and applications.
The primary goal of vulnerability assessment is to discover known security weaknesses before attackers can exploit them. It typically involves automated tools that scan systems for outdated software, misconfigurations, weak passwords, and other security flaws.
Instead of exploiting vulnerabilities, the process focuses on detecting and reporting potential risks.
Key Features of Vulnerability Assessment
- Automated scanning tools are used to identify vulnerabilities.
- It detects known security weaknesses based on vulnerability databases.
- Results are presented as a list of potential security risks.
- It provides recommendations for fixing identified vulnerabilities.
- It is usually conducted regularly to maintain system security.
Vulnerability assessments are useful for identifying large numbers of vulnerabilities quickly, helping organizations understand their overall security exposure.
What Is Penetration Testing?
Penetration Testing, often called Pentesting, is a cybersecurity testing method where ethical hackers simulate real cyberattacks to determine whether vulnerabilities can actually be exploited.
Unlike vulnerability assessments, penetration testing is usually manual and highly targeted. Security professionals attempt to exploit identified weaknesses to see how far an attacker could go in gaining access to systems.
The goal of penetration testing is to understand the real-world impact of security vulnerabilities.
Key Features of Penetration Testing
- Conducted by ethical hackers or penetration testers
- Simulates real cyberattacks
- Involves both manual and automated techniques
- Focuses on exploiting vulnerabilities
- Provides detailed reports explaining how attacks could occur
Penetration testing helps organizations understand how attackers might break into their systems and what damage they could cause.
Vulnerability Assessment vs Penetration Testing: Key Differences
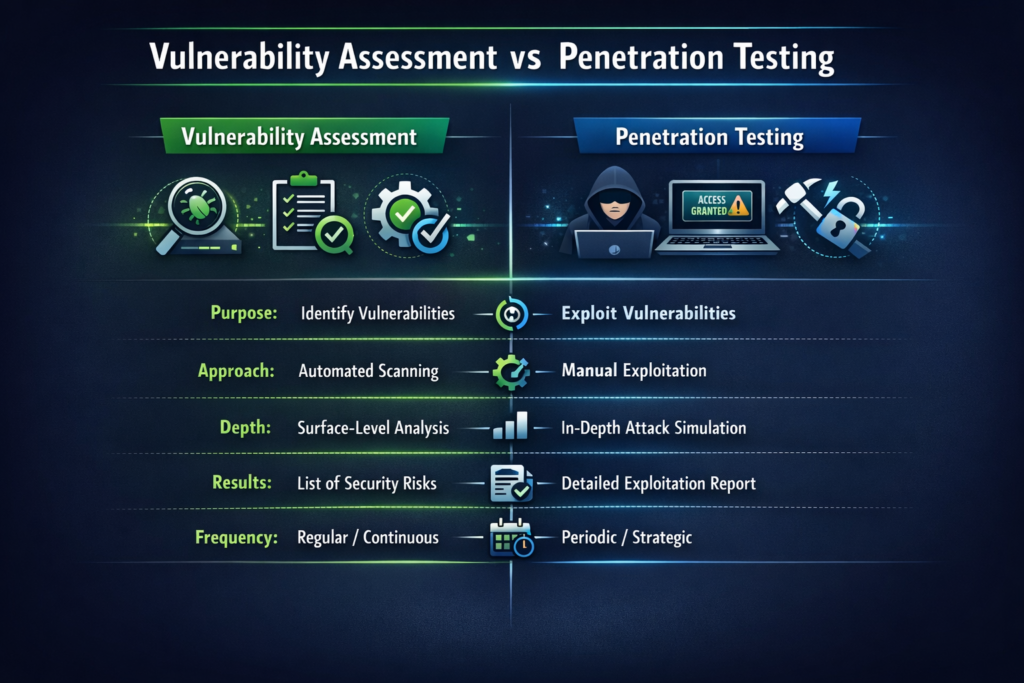
Although both methods aim to improve security, they differ in their objectives, techniques, and outcomes.
Difference in Purpose
Vulnerability Assessment focuses on identifying vulnerabilities across systems.
Penetration Testing focuses on exploiting those vulnerabilities to understand real attack scenarios.
Difference in Testing Approach
Vulnerability assessment relies mostly on automated scanning tools.
Penetration testing involves manual techniques and expert analysis to simulate attacks.
Difference in Depth of Analysis
Vulnerability assessments provide a broad overview of system weaknesses.
Penetration testing provides in-depth analysis of specific vulnerabilities.
Difference in Results
A vulnerability assessment produces a list of identified vulnerabilities.
Penetration testing provides detailed attack paths and exploitation results.
Difference in Testing Frequency
Vulnerability assessments are typically conducted regularly or continuously.
Penetration tests are conducted periodically or during major security reviews.
In simple terms, vulnerability assessments identify problems, while penetration testing demonstrates how serious those problems really are.
VAPT Testing: Why Organizations Need Both
Many organizations mistakenly believe that vulnerability scanning alone is sufficient. However, relying on only one testing method can leave systems exposed.
Both vulnerability assessments and penetration testing play important roles in cybersecurity.
Role of Vulnerability Assessment
- Identify large numbers of vulnerabilities quickly
- Maintain continuous monitoring of security weaknesses
- Provide an overview of an organization’s security posture
Role of Penetration Testing
- Determine whether vulnerabilities can actually be exploited
- Identify hidden weaknesses that automated tools may miss
- Understand how attackers might gain access to systems
Using both methods together allows organizations to detect vulnerabilities and verify their real-world impact.
Top Tools Used in VAPT
Cybersecurity professionals rely on several tools when performing vulnerability assessments and penetration testing.
Nessus
Nessus is one of the most widely used vulnerability scanners that identifies known vulnerabilities in systems and applications.
OpenVAS
OpenVAS is an open-source vulnerability scanning tool used to detect security weaknesses across networks.
Nmap
Nmap is a powerful network scanning tool used to discover hosts, open ports, and services running on a network.
Burp Suite
Burp Suite is a popular web application testing tool used by penetration testers to identify vulnerabilities in web applications.
Metasploit
Metasploit is a penetration testing framework used to exploit vulnerabilities and test system defenses.
These tools help cybersecurity professionals analyze systems and simulate attacks in controlled environments.
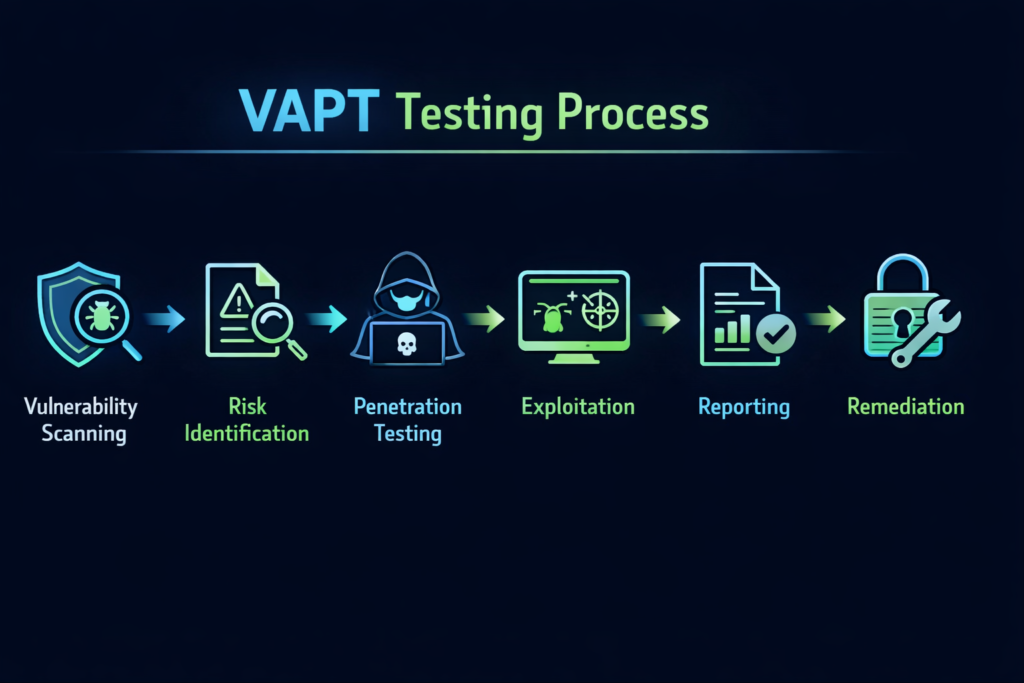
Real-World Example of VAPT Testing
Consider a company that operates an online shopping website.
First, a vulnerability assessment is conducted. Automated scanners identify several weaknesses, such as outdated software and misconfigured server settings.
Next, a penetration test is performed. Ethical hackers attempt to exploit the vulnerabilities discovered during the assessment. They may successfully gain unauthorized access to the system through a weak authentication mechanism.
This process shows the organization not only what vulnerabilities exist but also how attackers could use them in real-world scenarios.
Benefits of VAPT Testing for Businesses
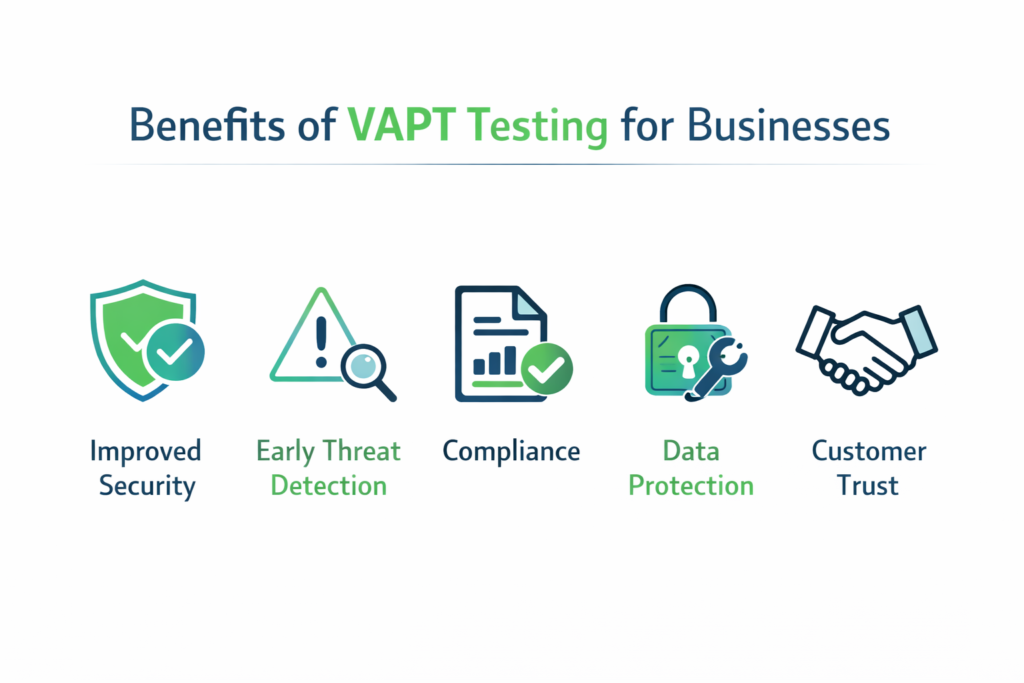
Organizations that regularly conduct security testing gain several advantages.
Improved Security Posture
Regular testing helps identify vulnerabilities before attackers can exploit them.
Early Threat Detection
Security teams can detect weaknesses early and apply patches before damage occurs.
Compliance with Security Regulations
Many industries require security testing to meet compliance standards such as PCI-DSS and ISO 27001.
Protection of Sensitive Data
Security testing helps prevent data breaches and unauthorized access.
Increased Customer Trust
Organizations that prioritize cybersecurity build stronger trust with their customers.
Conclusion: Vulnerability Assessment vs Penetration Testing Explained
In today’s evolving threat landscape, organizations must proactively test their systems to stay secure. Both vulnerability assessment and penetration testing play essential roles in identifying and addressing security risks.
A vulnerability assessment provides a broad overview of security weaknesses, while penetration testing goes deeper by simulating real cyberattacks to determine whether those vulnerabilities can be exploited.
Instead of choosing one over the other, organizations should use both methods together to build a stronger cybersecurity defense strategy.
