Introduction
Web security testing forms the cornerstone of modern application development, ensuring vulnerabilities do not expose user data or systems to exploitation. In 2026, with cyber threats evolving through AI-driven attacks and quantum computing risks, developers must prioritize rigorous web security testing to safeguard applications against breaches that cost organizations billions annually. This guide delivers a comprehensive checklist aligned with OWASP Top 10 standards, covering authentication, input validation, API protections, and more. By integrating these practices into development workflows, teams can mitigate risks, comply with regulations like GDPR and CCPA, and build resilient web applications that withstand sophisticated threats.

Fundamentals of Web Security Testing
Web security testing involves systematic vulnerability assessment to identify and remediate weaknesses in web applications before deployment. Developers conduct these evaluations during the software development life cycle (SDLC) to enforce secure coding practices, reducing the attack surface from inception.
- Establish a baseline with automated scanning tools integrated into CI/CD pipelines for continuous web security testing.
- Define testing scope covering frontend, backend, and infrastructure layers to ensure comprehensive coverage.
- Document findings in a centralized repository for tracking remediation progress and compliance audits.
- Train teams on threat modeling to anticipate attack vectors specific to application architecture.
- Schedule regular penetration testing phases, including both static and dynamic analysis.
Authentication and Authorization Testing
Authentication verifies user identities, while authorization controls access to resources, forming critical defenses against unauthorized entry. In 2026, testing these mechanisms prevents account takeovers amplified by credential stuffing and biometric spoofing.
- Validate multi-factor authentication (MFA) implementations resist bypass techniques like SIM swapping.
- Test password policies for strength requirements, including length, complexity, and rotation enforcement.
- Verify role-based access control (RBAC) restricts privileged actions to authorized users only.
- Assess session fixation and hijacking vulnerabilities through forced logouts and token regeneration.
- Confirm OAuth and OpenID Connect flows handle token validation, expiration, and scope limitations accurately.
Input Validation and Sanitization Practices
Input validation and sanitization protect against injection attacks by scrutinizing all user-supplied data. Proper implementation neutralizes threats like SQL injection and cross-site scripting (XSS), which remain prevalent in the OWASP Top 10.
- Enforce server-side validation for all inputs, rejecting malformed data before processing.
- Apply context-aware sanitization, such as HTML escaping for outputs and parameterization for queries.
- Test file uploads for size limits, type restrictions, and malware scanning integration.
- Validate API payloads against schemas to block deserialization exploits.
- Monitor for command injection by isolating execution environments and whitelisting allowed inputs.
API Security Testing Essentials
APIs drive modern web architectures, making their security paramount against exploitation via broken object-level authorization and excessive data exposure. Developers must test endpoints rigorously to align with standards like OWASP API Security Top 10.
- Examine rate limiting and throttling to prevent denial-of-service (DoS) attacks.
- Verify JWT and API key handling for signature validation and replay protection.
- Test for insecure direct object references (IDOR) by attempting unauthorized resource access.
- Ensure CORS policies restrict origins and methods appropriately.
- Audit GraphQL queries for introspection disabling and depth limiting.
Session Management Security Measures
Effective session management maintains state securely, thwarting hijacking and fixation attacks that undermine user trust. Testing focuses on token integrity and lifecycle controls in high-traffic 2026 environments.
- Implement secure, HTTP-only cookies with SameSite attributes to mitigate CSRF.
- Enforce short session timeouts with automatic renewal on activity.
- Test logout mechanisms for complete token invalidation across all devices.
- Validate secure flag usage on cookies in transit over HTTPS.
- Monitor for session prediction by generating unpredictable identifiers.
Data Protection and Encryption Protocols
Data protection through encryption safeguards sensitive information at rest and in transit, countering interception and ransomware threats. Developers test compliance with standards like TLS 1.3 and FIPS 140-3.
- Mandate HTTPS enforcement with HSTS headers to prevent downgrade attacks.
- Encrypt stored data using AES-256 with key rotation policies.
- Test database query encryption for field-level protections.
- Verify backup encryption and access logging for audit trails.
- Assess certificate management for revocation checking and chain validation.
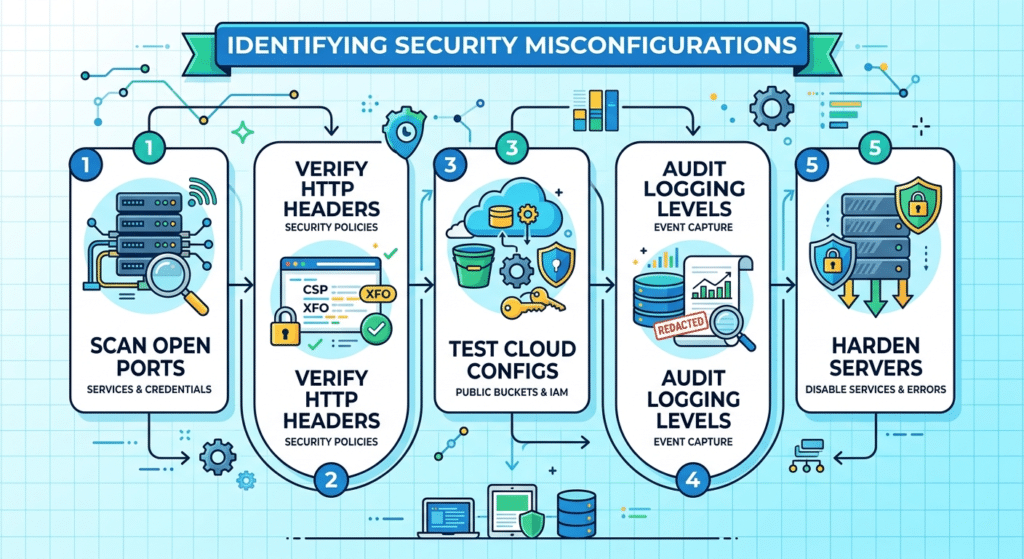
Identifying Security Misconfigurations
Security misconfigurations arise from default settings or overlooked updates, enabling attackers to exploit exposed services. Proactive testing uncovers these issues across servers, cloud, and frameworks.
- Scan for open ports, unnecessary services, and default credentials.
- Verify HTTP security headers like Content-Security-Policy (CSP) and X-Frame-Options.
- Test cloud configurations for public S3 buckets or misconfigured IAM roles.
- Audit logging levels for comprehensive event capture without sensitive data leaks.
- Harden servers by disabling directory browsing and error message verbosity.
Mitigating Dependency and Third-Party Risks
Dependencies introduce supply chain vulnerabilities, as seen in recent Log4Shell incidents. Developers assess third-party components for known exploits and maintenance status.
- Maintain an up-to-date software bill of materials (SBOM) for vulnerability tracking.
- Scan libraries with tools like Dependabot or Snyk before integration.
- Limit third-party script usage with subresource integrity (SRI) checks.
- Test for transitive dependencies introducing unpatched flaws.
- Establish vendor risk assessments for SaaS integrations.
Advanced Web Security Testing Checklist
Beyond basics, advanced web security testing addresses emerging 2026 threats like AI-generated payloads and zero-day exploits. This checklist builds on OWASP alignments for comprehensive coverage.
- Conduct business logic flaw testing for workflow manipulations.
- Simulate supply chain attacks on CI/CD pipelines.
- Test client-side protections against DOM-based XSS and prototype pollution.
- Evaluate WebAssembly modules for memory safety violations.
- Perform fuzzing on edge cases to uncover hidden injection points.
Integrating Web Security Testing into Development Workflows
Seamless integration of web security testing elevates it from an afterthought to a core practice, fostering a security-first culture. Developers embed checks at every stage for proactive defense.
- Automate static application security testing (SAST) in code commits.
- Incorporate dynamic application security testing (DAST) in staging environments.
- Use interactive application security testing (IAST) for runtime monitoring.
- Align with DevSecOps by shifting security left in the pipeline.
- Measure effectiveness through key risk indicators (KRIs) and regular audits.
Conclusion
Proactive web security testing in cyber security empowers developers to fortify applications against an ever-expanding threat landscape in 2026. By diligently applying this checklist from authentication validations to dependency audits teams assume responsibility for robust defenses, minimizing breach risks and ensuring user trust. Consistent implementation not only meets regulatory demands but also enhances application reliability, positioning organizations ahead of adversaries. Developers who prioritize these practices deliver secure, scalable web solutions that endure.
