Cyber threats evolve faster than most organizations can adapt, and few are as scalable or damaging as the botnet attack. A botnet attack weaponizes hundreds or thousands of compromised devices, called zombie devices, to carry out coordinated malicious campaigns under remote criminal control. From flooding servers with distributed denial-of-service traffic to silently harvesting credentials and deploying ransomware, botnets cause severe and wide-ranging damage. For ethical hackers, understanding this threat is foundational. Security professionals must simulate, analyze, and disrupt botnet infrastructure to stay ahead of black-hat operators. This post covers how botnet attacks function, the layered risks they present in ethical hacking contexts, and the strategies security teams deploy to neutralize them. Whether you work in penetration testing, threat intelligence, or incident response, this guide provides practical insight to build stronger, more proactive defenses starting today.
What Defines a Botnet Attack
A botnet attack occurs when threat actors hijack internet-connected devices and remotely control them through command-and-control servers. These zombie devices carry out spam distribution, credential theft, and denial-of-service floods without the owners’ knowledge. Ethical hackers study this architecture to understand how attackers build and silently scale malicious operations inside enterprise networks.
- Zombie devices include PCs, servers, smartphones, and IoT hardware across global networks
- C&C servers deliver commands and collect stolen data from all infected endpoints
- Botnets can contain millions of compromised devices spanning multiple countries simultaneously
- Attackers rent botnet access through dark web marketplaces for targeted criminal operations
- Minimal performance degradation on infected devices makes early detection extremely difficult
How Botnet Attacks Infiltrate Ethical Hacking Environments
Ethical hackers simulate botnet attack behavior in authorized environments to expose vulnerabilities before criminal operators find them. This involves replicating infection vectors and mimicking C&C communications under controlled conditions. Black-hat actors frequently repurpose the same tools ethical hackers rely on, which complicates the distinction between simulated and genuine intrusion traffic inside production networks.
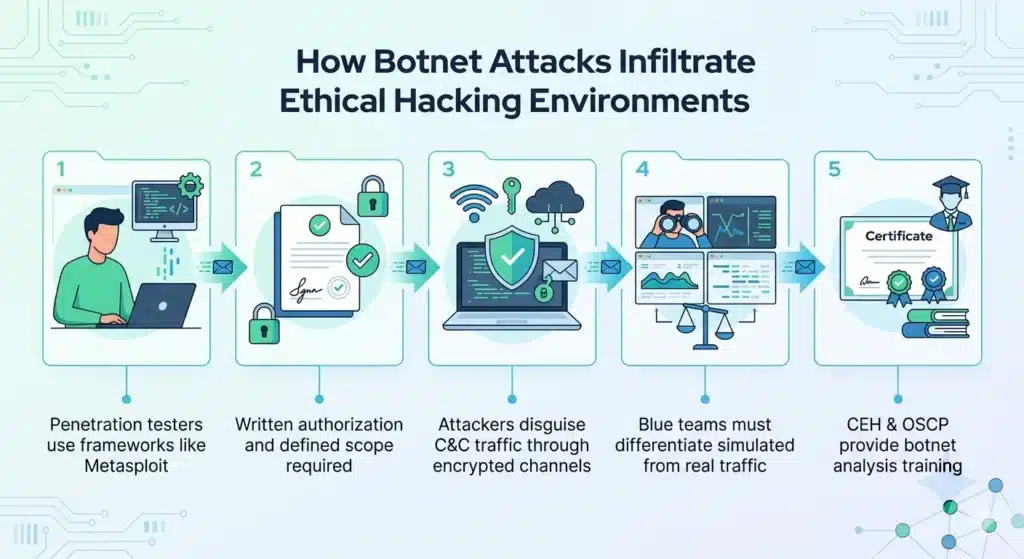
- Penetration testers use Metasploit and similar frameworks to safely replicate botnet behavior
- Written authorization and clearly defined scope are legally required for all botnet simulations
- Attackers disguise C&C traffic through encrypted channels to evade detection tools effectively
- Blue teams must differentiate simulated botnet traffic from real active compromise activity
- Certifications like CEH and OSCP include structured training on botnet attack analysis
The Role of Command-and-Control Servers
C&C servers are the operational core of every botnet. They deliver instructions, push malware updates, and collect stolen data from zombie devices across the network. Ethical hackers prioritize disrupting C&C infrastructure during takedown operations because neutralizing it cripples the entire network. Modern operators use peer-to-peer architectures and domain generation algorithms to make their infrastructure significantly harder to dismantle.
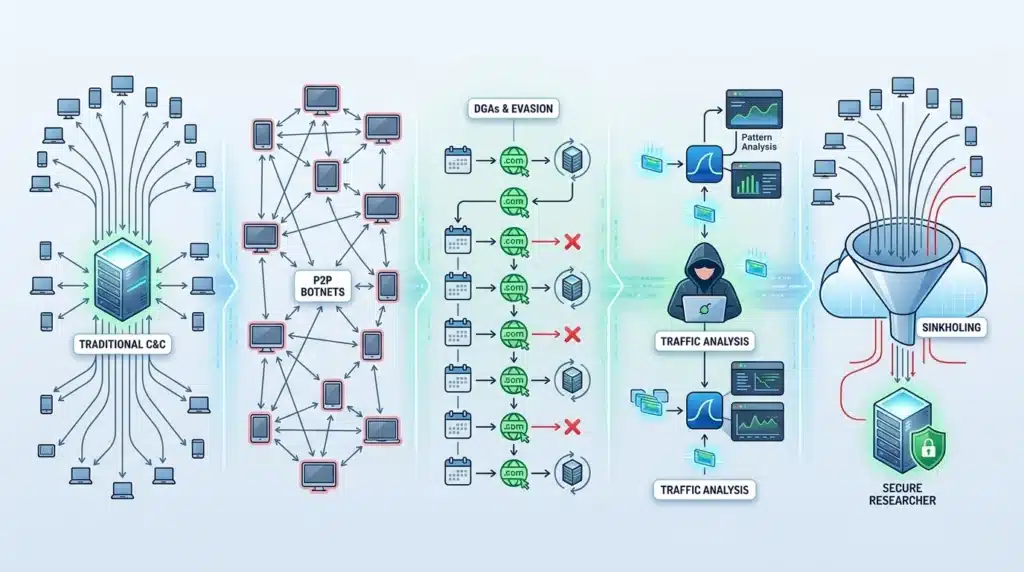
- Traditional botnets use centralized HTTP or IRC-based command-and-control communication channels
- Peer-to-peer botnets distribute control across infected nodes, eliminating single points of failure
- Domain generation algorithms allow C&C servers to cycle through addresses and evade blacklisting
- Ethical hackers use Wireshark to capture and analyze C&C communication patterns in detail
- Sinkholing redirects botnet traffic to researcher-controlled servers for behavioral analysis
Common Infection Vectors and Payload Delivery Methods
Botnet infections spread through phishing emails, drive-by downloads, exploit kits targeting zero-day exploits, and compromised software updates. Once infected, a device establishes persistence and connects to its C&C server to await instructions. Payload delivery is carefully staged to bypass antivirus detection and maintain a lasting foothold inside targeted systems and enterprise environments.
- Phishing emails remain the single most common botnet infection entry point globally
- Exploit kits automatically target zero-day vulnerabilities in browsers and widely used plugins
- Multi-stage loaders deliver final payloads covertly to avoid triggering endpoint security alerts
- Malvertising embeds malicious scripts invisibly inside legitimate advertising networks
- Enterprise environments also face infection risk through compromised removable media and network shares
Notable Botnets: Mirai Malware, Zeus, and Their Legacy
Mirai malware redefined the threat landscape by targeting IoT devices and launching record-breaking DDoS attacks against major internet infrastructure globally. Zeus botnet specialized in financial credential theft, affecting millions of banking users worldwide through keylogging and form grabbing. Both cases shaped how ethical hackers approach botnet threat modeling and inform defense strategy development across the industry today.
- Mirai exploited unchanged default credentials on IoT cameras, routers, and digital video recorders
- Zeus used keylogging and form grabbing to harvest financial credentials at enormous scale
- Necurs botnet distributed billions of spam and ransomware payloads across multiple years
- Emotet evolved into a full botnet delivery platform before law enforcement dismantled it in 2021
- Modern operators borrow and adapt techniques from all of these landmark historical predecessors
DDoS Amplification Through Botnet Infrastructure
Distributed denial-of-service attacks powered by botnet infrastructure overwhelm target servers with traffic volumes until they fail. Attackers amplify volume using DNS, NTP, or memcached reflection techniques, multiplying bandwidth without increasing their botnet footprint. Ethical hackers simulate these scenarios in authorized settings to measure how well a network absorbs and responds to volumetric traffic under stress conditions.
- Botnet-powered DDoS attacks can generate terabits of traffic per second at peak output
- Memcached-based amplification can multiply traffic volume by up to 51,000 times the request size
- Volumetric, protocol, and application-layer attacks each require entirely different mitigation approaches
- CDN services and rate limiting serve as critical front-line defenses against DDoS campaigns
- NetFlow-based analysis enables real-time detection of volumetric traffic anomalies across the network
IoT Vulnerabilities and Botnet Recruitment Tactics
IoT devices are the fastest-growing recruitment pool for botnet operators worldwide. Weak default passwords, unpatched firmware, and minimal security design make smart devices easy targets for automated scanners. Ethical hackers use tools like Nmap and Shodan during authorized reconnaissance to identify exposed IoT assets and enable clients to patch vulnerabilities before attackers exploit them at scale.
- Billions of IoT devices globally still operate with unchanged factory-default login credentials
- Shodan indexes publicly exposed devices, serving as a research tool for defenders and attackers alike
- IoT botnet infections often survive device reboots through firmware-level persistence mechanisms
- Segmenting IoT devices from core networks limits lateral botnet movement significantly after compromise
- Manufacturers must adopt secure-by-design principles to reduce exploitable attack surfaces industry-wide
Ethical Hacking Tools for Detecting Botnet Activity
Detecting a botnet attack requires specialized tools combined with behavioral analysis across the network. Wireshark identifies irregular outbound traffic signaling C&C communications. Nmap reveals unauthorized ports and services on internal hosts. SIEM platforms correlate logs across the entire environment to surface anomalies pointing to active compromise, giving security teams a comprehensive and actionable threat picture.
- Wireshark flags unusual outbound connection patterns linked to known C&C server addresses
- Nmap scans reveal unauthorized services and open ports running on internal network hosts
- Snort and Suricata apply signature-based detection rules to identify known botnet traffic patterns
- SIEM platforms correlate security events at enterprise scale to surface behavioral anomalies quickly
- Threat intelligence feeds deliver updated C&C IP lists and malicious domain inventories in real time
Ransomware Integration with Botnet Infrastructure
Modern ransomware campaigns increasingly rely on botnet infrastructure for large-scale payload distribution across target organizations. Botnets establish silent footholds inside environments days before ransomware deploys, allowing attackers to map critical systems and maximize encryption impact. Ethical hackers must understand this convergence to design detection workflows capable of intercepting threats before ransomware is triggered across the network.
- Botnet operators sell ransomware-as-a-service access to criminal affiliate networks for targeted campaigns
- Lateral movement through botnet-infected machines accelerates enterprise-wide ransomware deployment rapidly
- Endpoint detection and response platforms are highly effective at interrupting ransomware delivery chains
- Backup restoration testing is a critical component of ransomware defense in ethical hacking reviews
- Double extortion combines data exfiltration with encryption to increase leverage and pressure on victims
Botnet Takedown Operations and Long-Term Defense Strategies
Coordinated takedown operations bring together law enforcement agencies, ISPs, security vendors, and ethical hackers to systematically dismantle botnet infrastructure. Operation Tovar dismantled Gameover Zeus through sinkholing, domain seizures, and multi-agency intelligence sharing, proving that coordinated global response can neutralize even the most resilient and distributed botnet networks over time.
- Sinkholing redirects botnet traffic away from attacker-controlled C&C servers to neutralize operations
- DNS filtering blocks known malicious domains before infected devices reach C&C infrastructure
- Network segmentation limits the blast radius of any successful botnet intrusion significantly
- Security awareness training measurably reduces phishing-driven botnet infection rates across organizations
- Incident response plans must specifically address botnet detection, containment, and full remediation steps
Conclusion
Botnet attacks rank among the most persistent and damaging threats in modern cybersecurity. Their ability to scale across millions of devices, integrate with ransomware operations, and evade conventional detection tools makes them especially dangerous for organizations of every size. Ethical hackers play a vital role in exposing these threats through authorized simulations, detection-focused tool use, and active collaboration in takedown operations. Organizations must invest in IoT security hardening, network segmentation, threat intelligence integration, and ongoing employee training to meaningfully reduce their exposure. Learn more about DDoS mitigation and zero-day exploit defenses to strengthen your layered security posture. A proactive, ethically grounded security approach remains the most effective long-term defense against botnet attacks and the criminal ecosystems that sustain them.
FAQ
What is a botnet attack in ethical hacking?
In ethical hacking, a botnet attack is a simulated or analyzed threat where security professionals study how networks of zombie devices operate under remote criminal control. Authorized simulations help organizations identify and remediate security gaps before real attackers exploit them in production environments.
How do botnet attacks threaten organizational security?
They enable DDoS floods, ransomware delivery, credential theft, and mass spam campaigns simultaneously. A single compromised device can silently recruit others, expanding the botnet across corporate infrastructure and making early behavioral detection a critical defensive priority for security teams.
What tools do ethical hackers use against botnets?
Wireshark, Nmap, Snort, Suricata, SIEM platforms, and threat intelligence feeds are essential detection resources. Together they provide traffic analysis, port scanning, signature-based detection, and behavioral correlation that expose active botnet presence across enterprise network environments.
How can organizations reduce botnet infection risk?
Applying firmware patches, enforcing strong unique passwords, segmenting IoT devices, enabling DNS filtering, deploying EDR solutions, and running phishing awareness training all significantly reduce botnet attack exposure and limit the damage if a compromise occurs.
What made Mirai malware historically significant?
Mirai proved that poorly secured IoT devices could be weaponized at massive scale to execute some of the largest DDoS attacks ever recorded. Its emergence permanently changed how ethical hackers and security architects assess IoT risk within broader botnet threat modeling frameworks.
