ADIS
Advanced Diploma in Information Security
Enhance your knowledge of cybersecurity, threat intelligence, penetration testing, and incident response through hands-on training and real-world simulations.
14 Modules
12 Months
Explore our Course Curriculum
- Information Security Vs Cybersecurity
- Cybersecurity Basic Terminologies
- CIA Triad
- Cyberkill Chain
- Phases Of Hacking
- Phases Of Penetration Testing
- Ethics & Legal Considerations In Cybersecurity
- Security Policies,Standards & Best Practices
- Windows Vs Linux
- History & Evolution Of Linux
- Linux Distributions
- Linux Installation & Configuration
- File System Hierarchy & Directory Structure
- File & Directory Permissions
- Linux Basic Commands
- File System Maintenance & Troubleshooting
- Linux Shell Scripting
- Virtualization & Containers
- Types Of Computer Networks
- Networking Devices
- Networking Topologies
- Transmission Medias Standards & OSI Reference Model
- Networking Protocols
- Routing & Switching
- Troubleshooting
- Configuring Windows Server
- Active Directory Domain Services
- ADDS Account Creation & Management
- GPO Management & DHCP
- Windows Server Security & Encryption
- RAID Levels
- Kerberos
- Understanding The Role Of Offensive Security In Information
- Security
- Common Attack Vectors & Methodologies
- Basic Tools & Techniques
- Reconnaissance & Footprinting
- Scanning & Enumeration
- Gaining Access
- Maintaining Access
- Clearing Tracks
- Social Engineering
- Phishing Attacks
- Reconnaissance & Enumeration Techniques
- Osint & Social Engineering
- Target Discovery
- Enumeration Techniques
- Vulnerability Identification
- Service & System Exploitation
- Protocol Attacks
- Evasion Techniques
- Wireshark
- Spoofing
- Introduction To Web Application
- Fundamentals Of HTTP
- Configuring Web Application
- Importance Of Web Application Security
- Web Application Security Frameworks
- Methodology
- Planning Phase
- Attack/Execution Phase
- Post-Execution Phase
- Web Application Vulnerabilities
- Burp Suite For Pentesters
- Vulnerability Scanning
- Password Attacks
- SQL Injection
- XSS
- JWT Attacks
- CSRF
- SSRF
- OS Command Injection
- Directory Traversal
- Authentication Vulnerabilities
- Business Logic Vulnerabilities
- File Upload Vulnerabilities
- Information Disclosure Vulnerabilities
- Fuzzing & Directory Enumeration
- Multiple Ways To Banner Grabbing
- Web Shells & Reverse Shells
- Overview Of Active Directory
- Importance Of Active Directory Security
- Types Of Attacks Against Active Directory
- Reconnaissance & Information Gathering
- Attacking The Active Directory
- Kerberoasting
- Asreproasting Attacks Using Impacket
- Passthehash Attacks
- Maintaining Access
- Android Intro And Security Architectures
- Android Lab Setup
- Android Static Analysis
- Android Dynamic Analysis
- Decompiling Android Apks Using Jadx And Mobsf
- Exploiting Input Validation Flaws
- Testing For Insecure Data Storage
- Testing For Authentication & Authorization Flaws
- Testing Android Apks Using Drozer
- Frida Tools
- Objection
- API Architecture & Protocols
- REST & SOAP
- Authentication & Authorization
- JWT, OAuth & API Keys
- OWASP API Top 10
- Business Logic Flaws
- Rate Limiting & Access Control
- API Exploitation Techniques
- Malware Types & Classification
- Indicators of Compromise
- Static Malware Analysis
- Dynamic Malware Analysis
- Sandbox & Behavioural Analysis
- Introduction to Reverse Engineering
- Command-and-Control Analysis
- Introduction to LLMs
- Prompt Engineering
- Prompt Injection Attacks
- Data Leakage Risks
- Jailbreak Techniques
- AI Model Abuse
- Defensive Strategies
- Introduction To ISO 9001 & Cybersecurity
- Cybersecurity Frameworks & Standards
- Risk Management & Cybersecurity
- Information Security Management System(ISMS)
- Cybersecurity Controls & Measures
- Incident Response & Business Continuity Planning
- Employee Awareness & Training
- Supply Chain Management & Cybersecurity
- What Is Security Operation Center
- Security Information & Event Management
- Architecture & Components
- Logging Process
- SIEM Sizing
- SIEM Solutions
- Managed SIEM
- Splunk
- Log Creating Using Use Cases
- Incident Response Team
- Cyber Threat Intelligence
- Indicators Of Compromise
No. of Modules:
14
Course Duration:
12 Months
Modes:
Online & Offline
Certification:
Provided
Are You Confused About Your Career?.
Let Us Help You. Request a Call Back.
Course Overview
Why You Should Choose Our Course ADIS?
With new dangers and technology continually developing, the world of cybersecurity is always changing. Anyone interested in pursuing a career in offensive security or defensive security should start with this Advanced Diploma in Information Security course since it offers a thorough overview of the most recent methods and equipment used in the industry. This course will provide you with the information and practical experience you need to succeed, whether you’re just starting out or trying to improve your current skills

Master Industry Tools through Hands-on Learning


















Ready to Break Into Cyber Security?
Master practical skills, work on real scenarios, and prepare yourself for a successful career in security.
Our Placements
Students Who Turned Skills Into Careers




Transform Your Learning with Expert Guidance.
We are a leading institution dedicated to providing comprehensive and training in cyber security.
- Highly experienced and qualified Professional Trainers
- 7+ years of experience in Cyber Security and Ethical Hacking
- Guidance on Real-World Security Scenarios


What makes our courses a superior choice for learning?
Offenso offers expert-led cyber security training with practical learning, real-world scenarios, and career-focused guidance.
- Hands-On Penetration Testing with Realistic Labs
- Career-Oriented Learning for Cyber Security Professionals
- Real-World Attack Simulations and Security Challenges
Exclusive Access to Our ARC Community.
We are a leading institution dedicated to providing comprehensive and training in cyber security.
- Network with Experts
- Daily Updates on Latest News
- Access to Community Events
- Essential Resources
Ready to Break Into Cyber Security?
Master practical skills, work on real scenarios, and prepare yourself for a successful career in security.
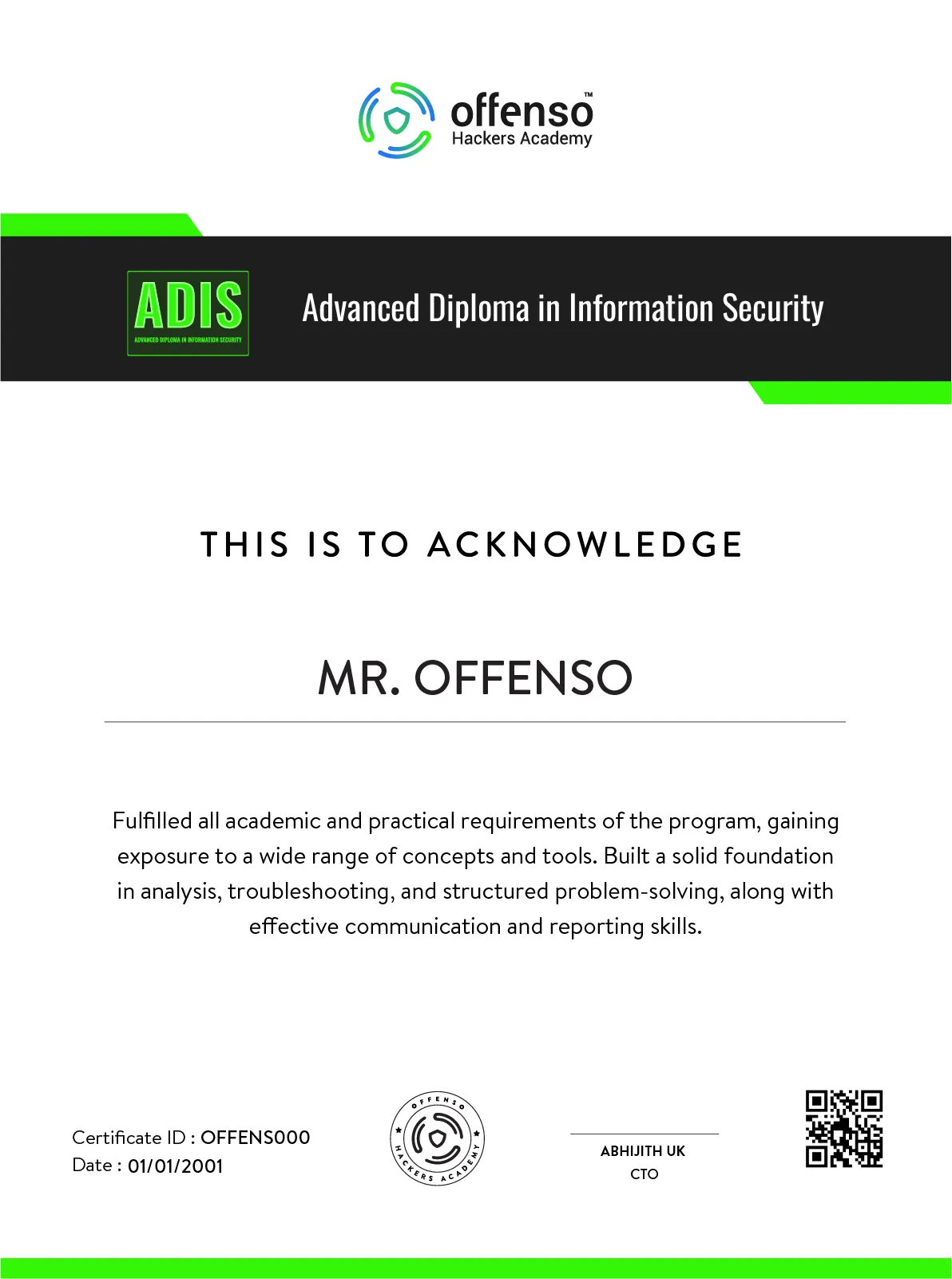
Get Certified
What Makes Our Courses a Superior Choice for Learning?
“Gain knowledge in information security with Offenso’s Certified Advanced Diploma in Information Security course. Enhance your knowledge of cybersecurity, threat intelligence, penetration testing, and incident response through hands-on training and real-world simulations. Earn a prestigious diploma, elevate your career, and become a key player in securing the digital landscape. Enroll now to unlock a world of opportunities in the dynamic field of information security.”
Student Testimonials
Let Our Students be Our Voice: Hear Their Stories, See Our Impact.
Together, we can make a difference and give our students the platform they deserve.
"I recently completed a course at the Offenso Academy and I am extremely satisfied with the education I received. The instructors were knowledgeable, and the course material was comprehensive and up-to-date. The Academy's emphasis on practical, real-world scenarios provided a unique and valuable learning experience that I would highly recommend to anyone interested in the field."
"I highly recommend the cyber security academy to anyone looking to pursue a career in cyber security. The program provided me with a strong foundation in both theory and practice, which allowed me to gain a deep understanding of the subject matter thanks to the cyber security academy, I feel confident in my ability to succeed in the field of cyber security and I am excited to apply what I have learned in my career."
Frequently Asked Questions
Looking for Answers about Cyber Security Education?
Find answers to your questions about our Advanced Diploma in Information Security course, designed for aspiring learners to gain cyber security expertise and practical skills.
The advanced Diploma in Information Security course is a combination of lecture-style lessons and hands-on labs and exercises.
The course is ideal for anyone looking to start a career in Cybersecurity or for IT professionals looking to enhance their knowledge and skills in the field of Pentesting.
For an Advanced diploma in Information Security course no prior knowledge of Cybersecurity is essential. The course is designed to provide comprehensive coverage of the subject, starting with the fundamentals and building up to more advanced topics.
The course is designed to be completed in 2 Months. Participants have to spend a minimum of 10 Hours in a week on coursework, including lessons, labs, and exercises.
Empowering Cyber Enthusiasts with Ethical Hacking Skills Start your Journey now
Graduates of Offenso Academy’s Advanced Diploma in Information Security programme will be well-equipped to begin rewarding jobs as network security administrators, cybersecurity consultants, or information security analysts. Students can be certain that they are receiving top-notch education and training to face the constantly changing problems of the cybersecurity landscape thanks to the academy’s reputation for generating knowledgeable and skilled experts. Throughout the program, students will engage in practical exercises and simulations, enabling them to identify vulnerabilities, assess risks, and implement robust security measures. The experienced instructors at Offenso Academy provide personalized guidance and mentorship to help students excel in this dynamic and fast-paced field.
Ready to Break Into Cyber Security?
Master practical skills, work on real scenarios, and prepare yourself for a successful career in security.




